Cyber Insurance Requirements: What You Need to Know
The global average cost of a data breach has soared by 15% to a staggering $4.45 million in 20231. This alarming increase highlights the severe threats in the digital realm and their direct impact on a company's financial health. With 71% of organizations now protected by cyber insurance1, it's crucial to understand how this insurance works and if it's essential for your business.
Data breaches and cyberattacks are on the rise, intensifying the need for robust data breach protection and business cyber insurance. To secure coverage, companies must meet strict cyber insurance requirements2. This includes implementing strong access controls, conducting proactive vulnerability assessments, and having a solid incident response plan.
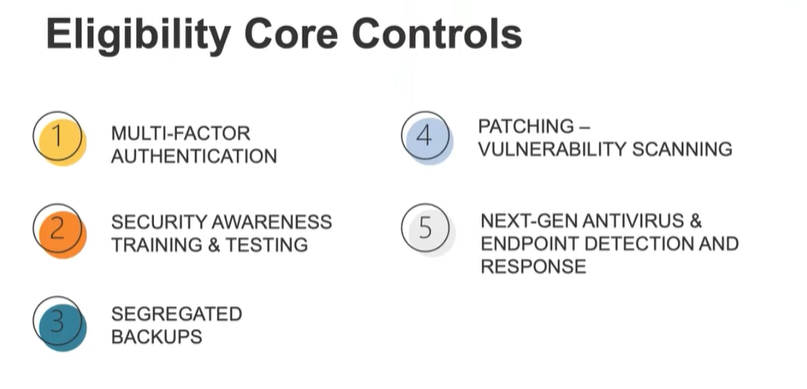
The cyberattack on ION Trading UK by a Russian ransomware gang has underscored the importance of these requirements2. Measures like employee cybersecurity training, multi-factor authentication (MFA), data encryption, and privileged access management are now essential for insurance eligibility.
The cyber insurance market is projected to surge from $12.5 billion to $116.7 billion by 20321. This growth underscores the urgency of implementing effective cyber protection strategies. Strategies such as MFA and data encryption not only strengthen defenses but also meet the stringent criteria set by insurance providers.
Key Takeaways
Understanding the evolving landscape of cyber security and the need for robust cyber insurance coverage.
Recognizing the rise in data breaches and cyberattacks as a bellwether for the need for comprehensive data breach protection measures.
Compliance with cyber insurance requirements can mitigate significant financial repercussions following a cybersecurity incident.
Understanding the “table stakes” for your business to meet insurance requirements.
Adopting cybersecurity best practices like MFA, data encryption, and regular employee training to satisfy insurance stipulations.
The expansion of the cyber insurance market suggests a heightened overall risk environment and an increasing recognition of insurance as a crucial risk management tool.
Understanding Cyber Insurance in the Era of Digital Threats
In today's digital-first world, grappling with cyber threats is a pervasive challenge for organizations across all sectors. The exponential rise in cyber incidents demands a robust cyber liability coverage plan designed to protect businesses from a spectrum of digital risks, from data breaches to cyberattacks.
The Rise of Cyber Insurance Post-Pandemic
Following the global upheaval caused by the pandemic, the reliance on digital technologies surged, inadvertently raising the stakes for cyber security. This shift was met with a significant rise in cyber insurance adoption. With cybercrime projected to cost the world $9 trillion annually by 20243, organizations are rushing to acclimate by beefing up their cyber insurance coverage requirements. Escalations in reported cyber incidence rates, such as the overwhelming 7 million complaints received by IC3 since its inauguration4, underscore the urgency and necessity of obtaining comprehensive cyber insurance.
What Cyber Insurance Typically Covers
Understanding what is cyber insurance and what it covers is crucial for businesses seeking to mitigate financial and operational risks. Typically, a robust cyber insurance policy encompasses coverage for data loss and recovery, loss of revenue due to business interruptions, and costs arising from cyber attacks such as phishing and ransomware. For instance, policies that cover ransomware are essential as the average ransom payment in recent incidents reached a staggering $1.85 million USD in 20235, emphasizing the high stakes involved in modern cyber threats.
Moreover, the aftermath of a cyber breach no longer places the burden of proof solely on insurance companies; businesses now must demonstrate their adherence to stated security measures4. This shift underscores a fundamental change in how cyber risks are managed and insured, with businesses required to maintain detailed records and implement risk reduction methodologies to secure and renew their cyber insurance policies.
| Aspect | Coverage | Impact |
|---|---|---|
| Data Loss | Covered | Recovery support for lost data ensures business continuity |
| Business Interruption | Covered | Compensates for revenue lost during downtime |
| Phishing Attacks | Covered | Financial protection against deceptive practices |
| Ransomware | Covered | Support with ransom payments and negotiations |
Facing digital threats with adequate cyber insurance is more than a precaution; it's a strategic imperative. Whether it's preventing the potential fallout from phishing scams or the devastating impact of ransomware, a well-tailored cyber insurance policy forms the backbone of a resilient digital defense strategy for today's enterprises.
Comprehensive Cyber Insurance Requirements for Businesses
In today's digital world, keeping up with insurance policy compliance requires strict adherence to cybersecurity rules and strong defenses. Companies must adopt comprehensive cyber insurance requirements to protect their operations from sophisticated cyber threats.
Mandatory Implementation of Strong Access Controls
Businesses need to enforce strong access controls to secure cyber insurance. This approach not only prevents unauthorized access but also boosts insurance policy compliance and meets cyber insurance requirements for vendors. With 88% of data breaches caused by human error6, effective access controls are key to reducing risks and securing sensitive data. This directly affects coverage limits and premiums.
Regular Vulnerability Assessments to Prevent Breaches
Regular vulnerability assessments are crucial for spotting security weaknesses that could lead to data breaches. These proactive steps are seen as vital by insurers for lowering the risk of claims denials, where 27% of claims were denied or only partially paid due to coverage exclusions6. Businesses that regularly assess their systems significantly improve their compliance with cybersecurity regulations. This keeps them in good standing for insurance policy coverage.
Given these facts, companies must strictly follow the cybersecurity measures outlined in insurance policies to avoid unexpected liabilities and ensure full coverage. By meeting these strict requirements, businesses not only shield themselves against cyber threats but also gain an advantage in securing favorable insurance terms.
Assessing Risk: The Role of Incident Response Plans in Cyber Coverage
As digital landscapes evolve, so do the challenges and sophistication of cyber threats. This makes the role of incident response plans in cyber coverage more critical than ever. An effective incident response plan is essential, not just for regulatory compliance but also for assessing cyber risks and determining cyber insurance rates. N8tive offers policy development services if you are needing assistance creating an Incident Response plan or other related security policies, please consider us as you work through this process.
The Importance of a Documented Incident Response Strategy
For businesses aiming to safeguard sensitive data and maintain operational continuity, a documented incident response strategy is crucial. This strategy outlines protocols for swift containment and mitigation of damages. Insurance providers examine these plans to gauge a company's readiness to handle and recover from cyber threats. Proper documentation is key in cyber insurance calculation, showing a proactive approach to minimize potential impacts on business operations and reputation.
Components of a Robust Incident Response Plan
A robust incident response plan must include a comprehensive approach to managing and responding to incidents effectively. This involves initial threat identification, containment strategies, eradication, and recovery steps. Detailed post-incident analysis is crucial to prevent future occurrences. Each phase is designed to streamline cyber policy claims and support the cyber insurance claims process.
For your business's financial safety net, strategic preparations are key. Cyber insurance policies typically range from $1 million to $5 million, based on your measures and potential risks7. Deductibles in these policies usually represent a percentage of the total loss7, highlighting the importance of robust mitigation and quick response capabilities.
Recent years have shown a pressing need for stringent incident response strategies. The Sony Playstation Network breach in 2011, without adequate cyber insurance coverage, resulted in losses of $171 million7. This financial hit underscores the critical nature of effective incident response plans to support cyber insurance claims and calculations.
Ensuring your incident response plan includes provisions for rapid action can be the difference between a manageable setback and a devastating breach. Insurance underwriters consider factors like this, especially in high-risk scenarios for ransomware attacks8. Such plans facilitate quick recovery and maintain compliance with insurance policy requirements, highlighting the interdependence of cyber resilience and cyber insurance.
In conclusion, as cyber threats evolve, so does the complexity of risk assessment models used by cyber insurers. Your incident response plan directly impacts how cyber insurance is calculated and the strength of protection offered to your enterprise.
Employee Training: A Crucial Factor for Cyber Liability Coverage
The cyber insurance landscape is rapidly changing, making employee training more vital than ever. As threats escalate, businesses must secure top cyber insurance policies and educate their workforce proactively. This approach is essential for meeting cyber insurance requirements.
Developing a Cybersecurity Awareness Culture
Building a cybersecurity-aware culture is key to not just adhering to insurance policies but also to the overall security of an organization. Data breaches often stem from human errors9. Therefore, comprehensive security awareness training (SAT) is crucial. It educates on security practices and threat detection, significantly reducing cybersecurity risks10.
This culture shapes employee behavior, ensuring they are vigilant about protecting digital assets. It's about instilling a sense of responsibility across the team. A common phrase used in encouraging a more security aware workforce is, “See something, Say something.”
Streamlining Training Process for Better Compliance
Effective risk management can lead to significant savings, impacting cyber insurance costs. Streamlining training not only meets cyber insurance requirements9 but also affects premiums. A structured approach introduces employees to identity access management (IAM) and data classification, enhancing security9.
Regular cybersecurity training cuts down on breaches due to human error, a leading cause of incidents9. It includes interactive modules that make learning easy and practical. Employees learn to spot phishing attempts, manage data, and handle suspected breaches effectively.
Investing in employee training proves the value of cyber insurance and can lower premiums. It answers the question: 'is cyber insurance necessary?' Indeed, strong training is as vital as the insurance itself.
"Investing in comprehensive training for your team does more than fulfill a requirement; it builds the frontline of defense against cyber incidents."
| Coverage Aspect | Role of Employee Training | Impact on Insurance |
|---|---|---|
| Data Breach Prevention | Reduces risk through better practices | May lower premiums |
| Incident Response Readiness | Improves speed and effectiveness of response | Enhances coverage effectiveness |
| Compliance with Regulations | Ensures adherence to data protection laws | Critical for policy validity |
Determining Cyber Insurance Coverage Limits and Premiums
Assessing the question, how much cyber insurance do I need?, requires a deep dive into your business's specifics. Small businesses typically opt for policies with $1 million in per-occurrence and aggregate limits, alongside a deductible of about $1,00011. It's essential to consider your data handling practices and the potential breach costs to determine the right coverage12.
Is cyber insurance expensive? The answer varies widely based on your company's revenue, industry, and data risk management. For instance, some customers pay around $145 monthly for comprehensive coverage11. Companies with higher revenues might face higher premiums due to a heightened risk of cyber attacks13.
Risk Assessment's Role in Cyber Insurance Costs
A detailed risk assessment is key to determining the coverage limits your business needs. Companies in sectors like healthcare, considered high-risk, may require coverage limits between $1 million and $5 million or more1113. The risk assessment is a key part of an evaluation which is vital for setting a cyber insurance rate that accurately reflects your exposure and security level13.
Investing in proactive cyber security can lower the risk of attacks and insurance costs. Companies with strong security measures often enjoy lower premiums, as they pose a lower risk to insurers13. Furthermore, effective incident response and management can significantly reduce financial losses, making premiums more justifiable12.
In conclusion, grasping the nuances of cyber insurance coverage limits and premiums tailored to your business's needs and industry is crucial. It's not merely about whether cyber insurance is costly. It's about ensuring your coverage adequately shields your operations from cyber threats while aligning with your budget.
Securing Data with Multi-Factor Authentication (MFA)
In today's digital world, businesses face an escalating threat from cyber-attacks. Therefore, robust defensive measures like multi-factor authentication (MFA) are crucial. MFA adds essential layers to security protocols, especially in remote work settings where traditional security boundaries no longer apply.
Protecting Your Network Beyond Just Passwords
MFA enhances network security by requiring multiple verification forms. This approach significantly lowers the risk of unauthorized access, even if a password is compromised. By incorporating security tokens, biometric verification, or unique one-time codes sent to mobile devices, your security infrastructure is significantly bolstered. Notably, MFA can block 99.9% of attacks from compromised accounts14. Moreover, implementing MFA can be as cost-effective as $3 per user, per month, making security upgrades financially feasible15.
The Integral Role of MFA in Remote Work Security
With the rise of remote work, MFA is crucial for protecting data outside traditional office settings. Businesses that neglect to adopt sufficient security measures, such as MFA, face severe consequences. Statistics show that 60% of companies that experience a cyberattack may shut down within six months due to recovery difficulties15. By implementing MFA, companies not only protect their assets but also strengthen their compliance with evolving cybersecurity regulations.
The significance of MFA is underscored by its impact on cyber insurance eligibility and ratings. Insurance providers increasingly demand MFA for coverage, acknowledging its effectiveness in reducing risk. Many policies now require MFA for remote network access, underscoring its value14. This compliance can lead to more favorable policy terms.
Does cyber insurance cover ransom payments? This often hinges on preventive measures in place before an incident, including MFA14. With ransom payments reaching as high as $40 million, as seen in the case of CNA Financial Corp14, rigorous MFA implementation provides a compelling argument during claims.
In conclusion, integrating multi-factor authentication into your cybersecurity strategy is vital for effective cyber protection. By fortifying your defenses with MFA, you enhance your firm's resilience against cybercrimes, align with cybersecurity regulations, and may benefit from better cyber insurance ratings.
Encryption Practices to Safeguard Sensitive Data
The digital world's growth has made encryption crucial for protecting data and securing sensitive information. This method not only keeps data safe from unauthorized access but is also key for meeting industry standards like HIPAA and SEC16. Encryption is vital for both data at rest and in motion, offering a strong defense against cyber threats17.
With cyberattacks on the rise, it's vital for businesses to know what their cyber insurance covers. Most policies now require encryption as a basic security step1617. Questions about ransomware coverage are common, leading insurers to closely examine companies' encryption use before offering coverage. Not having strong encryption can result in higher premiums or even denial of coverage16.
Using endpoint encryption on devices like laptops and smartphones is highly advised17. This method not only secures data but also helps companies meet regulatory standards16. A breach of these devices can lead to major data losses, making encryption a key risk reducer16.
| Encryption Type | Use Case | Benefits |
|---|---|---|
| Whole Disk Encryption | Portable devices security | Protects entire disk at once, essential for stolen or lost devices |
| Endpoint Encryption | Workstation data security | Helps meet compliance requirements, reduces breach risk |
| Network Transmission Encryption | Data in motion | Secures data sent over networks using protocols like HTTPS, SFTP |
| Email Encryption | Confidential communications | Secures sensitive information shared via email |
| Industry | 2024 Key Requirement | Expected Premium Adjustment |
|---|---|---|
| Healthcare | Strict adherence to HIPAA and HITECH | Increase due to data breach risks |
| Finance | Compliance with NIST CSF and ISO/IEC 27001 | Adjusted based on risk assessment outcomes |
| Retail | Enhanced payment security and PCI DSS compliance | Variable, depending on incident history |
In retail, securing transaction data is a major focus. PCI DSS compliance is crucial, affecting cyber insurance coverage costs. Insurers look at these factors to set premiums, reflecting the increased risks of cyber theft and financial fraud24.
Small and medium-sized businesses face a high risk of cyber attacks, making cyber insurance more important. Yet, only about 10 to 15% of these businesses have adequate coverage, showing a significant gap in risk management26.
The cyber insurance landscape in 2024 requires businesses across various industries to adopt comprehensive cybersecurity frameworks. Tailoring policies to specific, industry-related risks is essential. This strategic approach helps in mitigating risks and securing favorable insurance terms2524.
Cyber Insurance Assessment: Qualifying for the Right Policy
Grasping cyber insurance assessments and fulfilling cyber insurance requirements is vital for businesses aiming to safeguard their operations. The path to qualifying for cyber coverage starts with a detailed risk assessment. This step is pivotal for insurance firms to evaluate a company's cybersecurity strength.
What Insurers Look for During Risk Assessment
Before offering coverage, insurance firms meticulously evaluate a company's cybersecurity program. They focus on key aspects such as secure access control, firewalls, endpoint detection and response (EDR), and multi-factor authentication (MFA). These elements must meet the minimum insurance policy compliance standards. Furthermore, companies must show their dedication to cybersecurity by keeping systems and applications current and adhering to strict security guidelines like the NERC Critical Infrastructure Protection (CIP) regulations27.
Cyber insurance firms often demand documented and annually tested Security Incident Response Plans as part of their risk assessment28. Such planning is crucial for organizations to effectively manage and lessen the impact of cyber incidents. N8tive offers policy development services if you are needing assistance creating an Incident Response plan or other related security policies, please consider us as you work through this process.
Effectively Demonstrating Your Security Posture
To qualify for cyber insurance coverage, your company must demonstrate effective network traffic management and constant monitoring. Implementing advanced services like Managed Detection and Response (MDR) is essential for identifying and responding to threats in real-time, aligning with common cyber insurance requirements28. Moreover, regular security awareness training and thorough employee testing are crucial to lower the risk of cyber attacks28.
Understanding the extent of coverage is equally crucial. Most affirmative cyber insurance policies cover a broad range of incidents, from data breaches and cyber theft to network security liabilities28. With the cybersecurity insurance market expected to expand, ensuring your business meets the necessary cyber insurance requirements can shield you from digital threats and severe financial losses linked to data breaches and cyber incidents29.
By maintaining a rigorous security stance and adhering to the detailed criteria set by cyber insurers, you can secure the appropriate policy. This approach will help you effectively mitigate risks and ensure your organization remains resilient against the dynamic cyber threat landscape.
Tailoring Cyber Policies: Addressing Unique Organizational Needs
As digital threats evolve, it's critical that cyber insurance requirements customized solutions are tailored to meet the unique challenges and operational specifics of your organization. Customizing your cyber policy isn't just about compliance; it's about ensuring your coverage mirrors the very risks you face daily. Whether you're a bustling e-commerce giant or a nascent startup, understanding who needs cyber insurance tailored to their specific situation is the cornerstone of effective risk management.
The best cyber insurance policies respond not just to generic risks but to particular vulnerabilities of a business sector or operation scale. For instance, data handling practices significantly influence premium costs, with organizations showing robust security measures often benefiting from lower premiums30. Moreover, industries such as healthcare and financial services may see increased requirements due to regulatory mandates31.
Understanding the coverage spectrum is vital. Does cyber insurance cover ransom payments? Indeed, it does, along with expenses related to cybersecurity breaches such as forensic investigations and legal fees32. However, note that policies rigorously define what constitutes a covered act and may exclude specific scenarios like known breaches prior to the policy purchase or regulatory fines where compliance was neglected31.
For a policy to be effective, it must align with your business's current cybersecurity posture and anticipated risks. Using predictive modeling and threat intelligence, insurers can offer coverage that reflects your business's real-time threat landscape, ultimately enhancing your preparedness and resilience against cyber threats30.
"Customized cyber insurance solutions" are not only advisable—they are imperative. By collaborating with reputable insurers who understand the nuances of your industry and technological dependencies, you can harness a cyber insurance framework that does more than respond to incidents—it prevents them.
Your business deserves a cyber insurance policy that grows with you, adapts to the evolving digital threats, and offers peace of mind knowing that, in the event of a cybersecurity incident, your operations can recover swiftly and securely. Start by assessing your current risk profile and security measures, then consult with our cybersecurity experts to tailor a program that addresses your unique needs and risk exposures comprehensively.
Coverage Exclusions and Policy Limitations
It's essential for businesses to grasp the details of coverage exclusions and policy limitations when considering cyber insurance. Knowing what your policy doesn't cover is just as crucial as understanding what it does protect. This knowledge is key to effectively managing financial losses from cyber incidents.
Navigating Exclusions to Avoid Coverage Pitfalls
Exclusions in cyber insurance policies can vary widely, from specific cyber attacks to damages outside the digital realm. For instance, ransom payments have surged from $812,000 in 2022 to over $1.54 million in 202333. This rise underscores the importance of evaluating whether your policy's exclusions might leave your business exposed. Moreover, there's a 27% chance that exclusions could block a payout for data breach claims34. Exclusions for war and terrorism, for example, might not cover damage from hostile actions, a critical concern for businesses in volatile areas35.
Understanding the Role of Coverage Limits in Claims
Coverage limits are crucial when filing cyber insurance claims. They set the maximum amount insurers will pay, affecting the extent of your reimbursement after a cyber event. With the average cost of recovering from a ransomware attack at about $1.82 million33, it's vital to ensure these limits can cover potential risks. Assessing the adequacy of these limits is a critical step in managing cyber insurance needs.
While the limitations and exclusions of your cyber insurance policy may seem overwhelming, they are vital to understanding and mitigating cyber risks. Ensuring your policy covers ransomware recovery without financial shortfalls and navigating the complexities of cyber insurance requirements is crucial. Being well-informed about these aspects significantly impacts your decision on whether cyber insurance is worth it.
Cyber Insurance Requirements: Comprehensive Cyber Security Measures
Your business’s security program must harmonize with the stipulations of cyber insurance. This entails showcasing a deep dedication to comprehensive security measures, encompassing effective vulnerability management. Insurers scrutinize whether potential clients possess proactive systems for identifying, categorizing, and neutralizing security threats. Lack of such management often results in application denial, underscoring the importance of a robust security stance36.
Furthermore, multifactor authentication (MFA) is now fundamental for safeguarding sensitive data and systems. By integrating MFA, you significantly bolster your cybersecurity by necessitating users to furnish multiple verification factors, thereby reducing unauthorized access risks36. Besides MFA, insurers evaluate the presence of Endpoint Detection and Response (EDR) or Managed Detection and Response (MDR) systems, which are pivotal in modern cybersecurity strategies36.
Insurance Providers' Expectations of Multifactor Authentication
The emphasis on multifactor authentication stems from the escalating threat environment, where conventional security measures are insufficient. The 2022 data reveals a 38% surge in cyberattacks, underscoring the imperative for advanced authentication methods37. MFA not only fortifies access but also satisfies insurance providers' escalating demands for enhanced access control as part of the cyber insurance requirements.
Adopting and sustaining advanced cybersecurity measures such as MFA is challenging but crucial for fulfilling insurers' stringent criteria. These criteria are becoming more demanding and are frequently being updated to address emerging security challenges.
Separating backups from the primary environment and conducting regular employee training significantly boosts a business’s eligibility for cyber insurance. These actions are crucial in demonstrating a proactive stance towards cybersecurity management, a quality highly esteemed by insurers36.
Adhering to the evolving cyber insurance standards necessitates a continuous evaluation of your security practices and alignment with the latest threats and preventive technologies. Collaborating with seasoned cybersecurity specialists can facilitate this process, ensuring your organization not only meets but surpasses the cyber insurance requirements. This approach protects your financial and operational interests against the escalating cyber threats.
Conclusion
The question of whether cyber insurance is mandatory takes a backseat to its undeniable need. While not legally mandated, many businesses now see it as crucial for bolstering their security and managing risk. The global cyber insurance market is expected to grow at a staggering rate of over 25% annually by 202638. This highlights the pressing need, especially for small to medium enterprises, where only 38% are currently covered38. Companies that develop robust incident response plans not only improve their readiness but also enjoy lower insurance premiums, up to 30%38.
The financial impact of cyber attacks can be enormous; for example, financial institutions face an average cost of $5.85 million38. In the U.S., the average cost is significantly higher, at $9.44 million, underscoring the significance of cyber insurance39. This underscores the importance of adhering to cyber insurance standards and investing in the right policies. Moreover, recognizing the role of internal security measures can help prevent 27% of cyber incidents, attributed to insider threats38.
When exploring cyber insurance options, it's crucial to be well-informed to find coverage that matches your organization's risk profile. Cyber insurance providers often demand high standards, sometimes requiring certifications like ISO 2700139. By securing the right coverage, your business can not only find peace of mind but also a strong defense against cyber threats. Embracing cyber insurance puts your organization in the 47% of companies that are proactively addressing cyber risks40, fostering a culture of resilience.
FAQ
What are cyber insurance requirements?
Cyber insurance requirements are the criteria set by insurance providers for coverage. These include strong access controls, regular vulnerability assessments, and an incident response plan. Additionally, policies often require employee training, multi-factor authentication, data encryption, and managing privileged access. Compliance with cybersecurity regulations and industry-specific requirements is also necessary.
How does cyber security insurance work?
Cyber security insurance provides financial support for various cyber incidents, like data breaches and ransomware attacks. It covers recovery costs, legal fees, customer notification, credit monitoring, and business interruption losses. Coverage depends on the company's cybersecurity practices and compliance with the insurer's requirements.
Is cyber insurance required?
Cyber insurance is not mandatory for all businesses but is highly recommended, especially for those handling sensitive data or at risk of cyber attacks. It's a crucial part of risk management as cyber threats increase. Certain contracts or regulations may require it.
What typically is included in business cyber insurance?
Policies cover costs for responding to cyber events, including data recovery, system repairs, legal services, and notification costs. They may also include business interruption coverage for lost revenue during system downtime. Some policies offer forensic analysis and incident response support. You will need to talk with your insurance provider to determine if they have specific Cyber Security firms they require you to work with during an incident.
How much cyber insurance do I need?
The amount of cyber insurance needed varies by business size, industry, data type, cybersecurity posture, and risk profile. A thorough risk assessment and consultation with insurance experts can help determine the right coverage limits.
How is cyber insurance calculated?
Premiums are based on a business's risk profile, including industry, company size, data exposure, security measures, claims history, and coverage range. Insurers may audit a company's cybersecurity practices to set premiums.
Does cyber insurance cover ransom payments?
Some policies cover ransom payments in ransomware attacks, but coverage varies among insurers and may have conditions or exclusions. Policyholders should review their policy to understand ransom payment coverage.
Does cyber insurance cover ransomware?
Yes, many policies cover ransomware attacks, including attack costs, data restoration, business interruption, and sometimes ransom payments, under policy terms and conditions.
Does cyber insurance cover phishing?
Cyber insurance covers phishing attacks, which can cause financial losses, data breaches, and other cyber events. Coverage includes investigation costs, legal fees, and restitution for those affected.
Who needs cyber insurance?
Any business using electronic networks, storing sensitive data, or operating online should consider cyber insurance. It's essential for companies of all sizes in various industries, especially those handling personal or financial data. In today's digital world, cyber insurance is a critical safeguard against cyber threats.
Source Links
https://services.hummingbirdnetworks.com/blog/understanding-cyber-insurance-a-comprehensive-guide
https://www.christensengroup.com/article/a-complete-guide-to-cyber-insurance
https://www.crowdstrike.com/cybersecurity-101/cyber-insurance/
https://www.auvik.com/franklyit/blog/cybersecurity-insurance-requirements/
https://www.sseinc.com/blog/cyber-insurance-incident-response-planning/
https://www.coalitioninc.com/topics/5-essential-cyber-insurance-requirements
https://expertinsights.com/insights/security-awareness-training-for-cyber-insurance/
https://www.insureon.com/small-business-insurance/cyber-liability/how-much-cyber-liability-do-i-need
https://www.ftc.gov/business-guidance/small-businesses/cybersecurity/cyber-insurance
https://www.crcgroup.com/Tools-Intel/post/multi-factor-authentication-a-must-have-for-cyber-coverage
https://blog.charlesit.com/what-does-encryption-mean-for-compliance-and-cyber-insurance
https://ksa-insurance.com/blog/best-practices-data-protection/
https://delinea.com/what-is/privileged-access-management-pam
https://www.tcs.com/insights/blogs/data-breach-cyber-insurance-regulations
https://www.fortinet.com/resources/cyberglossary/cyber-insurance
https://www.worthinsurance.com/post/the-fundamentals-of-cyber-insurance
https://www.intelice.com/cyber-insurance-requirements-in-2024-what-you-need-to-know/
https://www.coalitioninc.com/topics/cyber-insurance-policy-coverages
https://www.tufin.com/blog/navigating-cyber-security-insurance-requirements-comprehensive-guide
https://www.esentire.com/how-we-do-it/use-cases/meet-cyber-insurance-requirements
https://www.at-bay.com/articles/cyber-insurance-underwriting/
https://travasecurity.com/cybersecurity-insurance-requirements
https://business.ncccc.com/news/details/a-professional-guide-to-cyber-liability-insurance-10-15-2023
https://prowritersins.com/cyber-insurance-blog/how-does-cyber-insurance-work/
https://www.mahoneygroup.com/cyber-insurance-policy-exclusions/
https://www.cybershure.com/blog/demystifying-cyber-insurance-requirements
https://www.proofpoint.com/us/blog/email-and-cloud-threats/what-to-look-for-cyber-insurance-coverage
https://www.koop.ai/blog/what-cyber-insurance-requirements-to-expect